
AI security
Identify and mitigate AI-specific risks before they impact your business.
Structured audit, compliance alignment, and technical hardening for production AI systems.
years of AI dev experience
years in tech consulting
clients worldwide
Identify and mitigate AI-specific risks before they impact your business.
Structured audit, compliance alignment, and technical hardening for production AI systems.
years of AI dev experience
years in tech consulting
clients worldwide
Here is who we help to secure AI:
Customer trust depends on how safely your features handle data.
The more systems AI touches, the more control you need.
Education, healthcare, and legal organizations face strict oversight where AI security directly affects compliance.
Future compliance starts with security decisions made today.
AI exposure isn’t limited to four categories. If you’re building, deploying, or scaling AI – security should be part of the plan. And we are here to build it.
Artificial intelligence security gaps can quickly turn from technical failures into financial, compliance, and reputational losses. Below are the most common risks and how they affect your business:
Manipulated, low-quality, or intentionally corrupted training data leads to biased outputs, unstable behavior, and wrong business decisions.
Our response:
Validated ingestion pipelines, data lineage tracking, strict input controls, and continuous dataset integrity monitoring.
Unprotected models and exposed APIs can be copied, reverse-engineered, or abused through uncontrolled access to model endpoints.
Our response:
Model access restrictions, API protection, hardening techniques, rate limiting, and monitoring of inference activity.
Carefully crafted inputs, including prompt injection attempts, can distort outputs, trigger unintended behavior, or enable data exfiltration.
Our response:
Adversarial testing, robustness checks, secure prompt design, output filtering, and defensive model tuning.
External models, datasets, libraries, or AI vendors may introduce hidden vulnerabilities, licensing issues, or compliance exposure.
Our response:
AI component audits, dependency review, vendor risk assessment, and licensing verification.
Uncontrolled internal use of AI tools, including generative systems connected to business data, increases the risk of GDPR breaches and non-compliance with the EU AI Act.
Our response:
AI usage governance policies, access controls, monitoring mechanisms, and compliance readiness assessments.
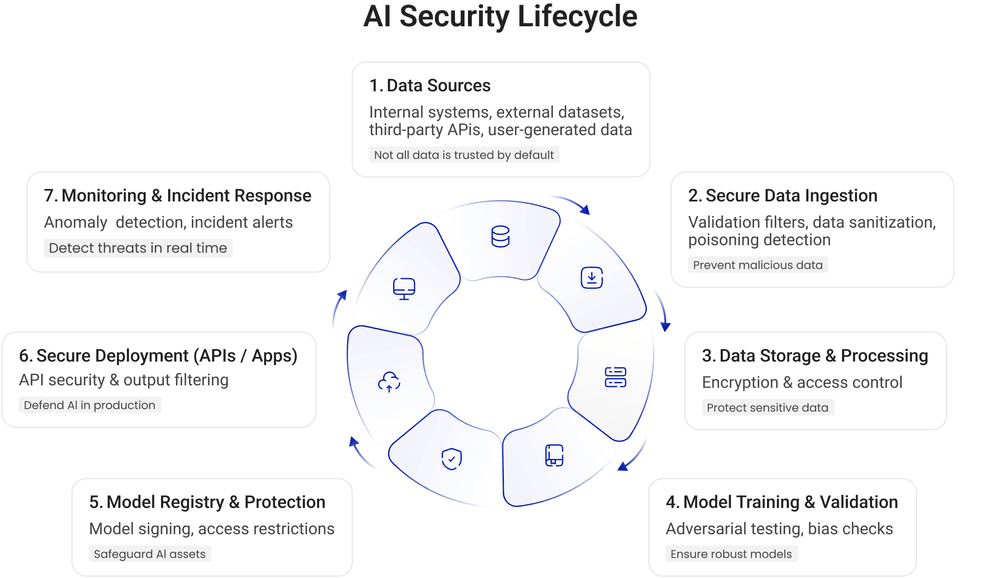
We provide not just security for AI – but security across its entire lifecycle. Here are what our services include:
“Find the weak spots before attackers do.”
We assess your AI across data, models, infrastructure, and third-party components to identify vulnerabilities and compliance gaps.
What you receive:
“Go live with confidence.”
Before deployment, we conduct a focused security and compliance review to reduce risk at launch.
Scope includes:
“Set the rules before problems appear.”
We define ownership models, access controls, and risk policies that shape how your AI operates and stays compliant.
Includes:
“Protect what you’ve built.”
We design and secure AI pipelines from data ingestion to production deployment, closing gaps before they turn into incidents.
Covers:
“Stay ready for what’s next.”
We monitor AI systems in production, detect anomalies or misuse, and prepare clear response scenarios.
Includes:
We map your AI systems to uncover vulnerabilities in models, data, integrations, and third-party tools.
We focus on what truly matters, ranking threats by business, compliance, and reputational impact.
Protection is built into data flows, models, and deployment pipelines from day one.
Before launch, we stress-test AI behavior and close gaps to reduce exposure.
We track AI in real time to detect misuse, anomalies, and drift as systems evolve.
Security adapts alongside your AI, updating safeguards and controls as threats and regulations change.
We’ve compiled everything you need to know about AI threats in our whitepaper. Learn how to identify vulnerabilities and protect your systems.
Every AI we build is protected from day one. Here’s how our security principles apply in real-world scenarios.
A mid-sized logistics company with a growing in-house legal department responsible for managing NDAs, service agreements, and vendor contracts across multiple regions.
The Aristek team developed an AI-powered solution to streamline veterinary medical record processing, enhancing efficiency and decision-making for veterinarians. The smart AI co-pilot functions as an add-on and can be easily integrated into various platforms, including any modern ai veterinary software platform.
A SaaS eLearning platform wanted to automate their customer support. We developed a chatbot that takes care of routine tasks and helps support specialists handle complex tickets.
A retail giant with 3 million customers sought to leverage their user data for sales forecasting. We used AI to analyze customer activity through advanced customer behavior analysis and applied ABA forecasting methods to generate accurate sales predictions and store insights.
Discover how a US telecom leader cut call center load by 40% with an AI-powered document assistant.
Our AI security approach follows established international frameworks that define how risks are identified, measured, and mitigated. This gives your organization structured controls, audit readiness, and confidence in front of regulators and enterprise clients.
Here’s how we organize security from the first byte to the final output.
Investing in artificial intelligence creates the conditions for stable growth and confident adoption.
Proactive controls reduce the likelihood of breaches, regulatory fines, and expensive recovery efforts.
Robust security supports compliance with data privacy and emerging AI governance standards.
Protected and explainable AI strengthens confidence among customers, partners, and regulators.
Hardened pipelines reduce downtime, unpredictable behavior, and production failures.
When security is embedded into architecture and workflows, teams can launch and scale AI solutions with confidence.
There are many AI security providers. Here are the reasons why you should collaborate with Aristek:
We follow GDPR, CCPA, the EU AI Act, and security best practices and frameworks like NIST, ISO/IEC 27001, and OWASP to ensure compliance and protection at every level.
Our team understands the security challenges of AI in eLearning, healthcare, petTech, retail, and beyond. We tailor solutions to meet industry needs.
Our experts aren’t just AI developers – they research, test, and innovate to stay ahead of threats. Security is built into everything we do.
We don’t just audit and leave. We take responsibility for your AI security from assessment to long-term stability, strengthening your architecture, not just patching gaps.
95% of our experts hold BS, MSc, or PhD degrees. 88% are Middle or Senior level, with most working here for over five years.
We rely on proven internal frameworks, audit templates, and security playbooks that speed up assessments and implementation without sacrificing quality.
Besides AI security services, we provide a range of AI-related services to help organizations develop, integrate, and optimize intelligent solutions.
We design and build custom AI models, applications, and solutions tailored to your business needs.
Our experts advise on AI strategy, governance, and adoption to maximize value and minimize risks.
We conduct research and prototype AI solutions to test their viability or accelerate innovation.
We connect AI solutions with existing systems and workflows to ensure seamless deployment and operation.
We use third-party cookies to improve your experience with aristeksystems.com and enhance our services. Click either 'Accept' or 'Manage' to proceed.